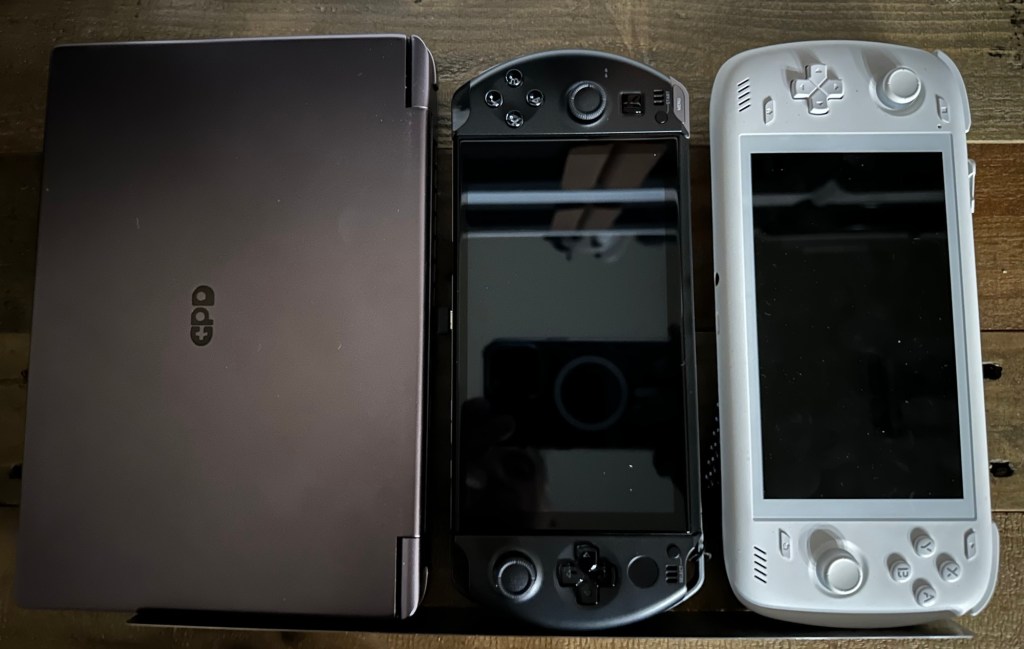
Windows or Android? Ayn Odin 2 vs GPD Win 4? Cost aside, it’s a tougher question than you might think! With “I’m a giant Switch Lite!”, and “I’m an overweight Vita!” styling respectively, both of these are chonky b0is, though still solidly in the realm of “easily portable”, if not “pocketable”. The answer of “which one?” probably comes down to priorities, or maybe even “why not both?”
The Ayn Odin 2 really shows the potential of Android as a gaming platform. It’s surprisingly polished out of the box, with a very bare bones install of Android (thankfully). The OEM software for device management, including controller configuration and screen mapping, is well designed and implemented, and rounding out the software package is a custom launcher that is well optimized for the gaming use case.
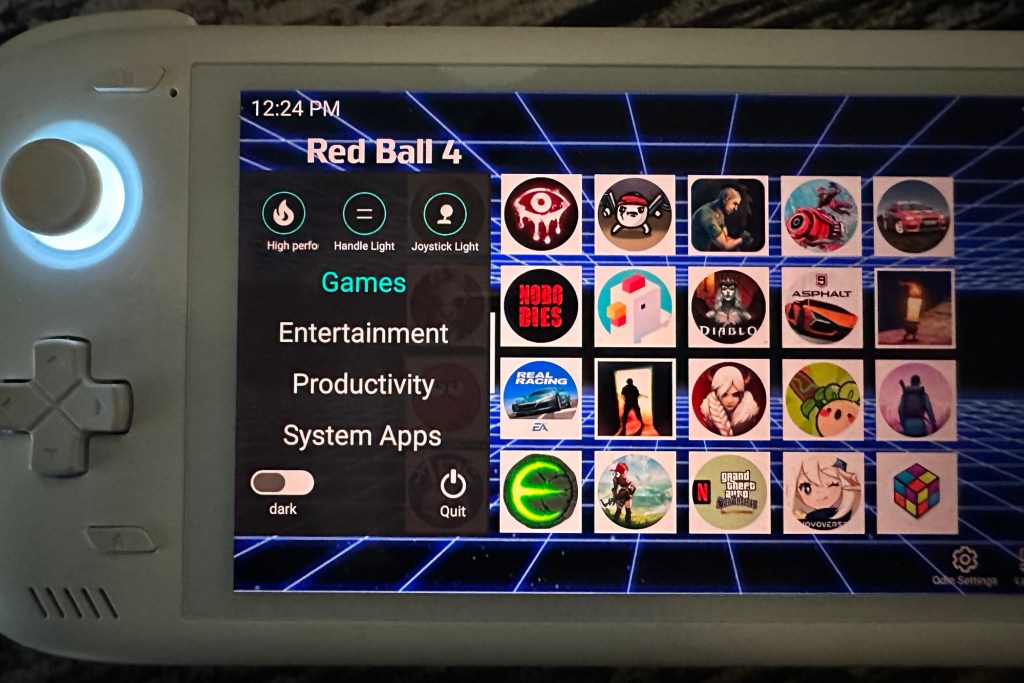


This particular Odin 2 is the Max variety, and with a Snapdragon 8 Gen 2, 16GB RAM, and 512GB of fast storage, and a MicroSD slot, there is more than enough power on tap for not just anything Android native, but the majority of emulation cases as well.



MicroSD performance is par for the course, with decent enough results from the SanDisk Ultra 1.5TB.

In terms of form factor the Odin is pretty big at 8.86 x 3.86 x 0.67 inches, which is inevitable given the 6”, 1080P, IPS screen and candy bar form factor, but it’s also quite light at only ~15oz (420g). Ergonomics are fantastic, with that light weight certainly playing a factor, leading to no hand fatigue even for long sessions. The controls are excellent as well, with Ayn having made the wise decision to implement Hall sticks as well as a PlayStation style dpad and Y/X/A/B buttons, stacked shoulder triggers, front home/start/select/play buttons, and even two handy rear buttons. Audio is served up by two decent enough front firing speakers, or through the 3.5mm phono jack. One USBC and a mini HDMI port round out the I/O. Rounding out the packaging is excellent comfortable RGB ambient lighting on the hall sticks and each side of the device, and vents both top and rear (with active cooling via controllable fan) for thermal management. Also noteworthy is that the device feels solid and high quality, significantly better than devices from other manufacturers in this category.
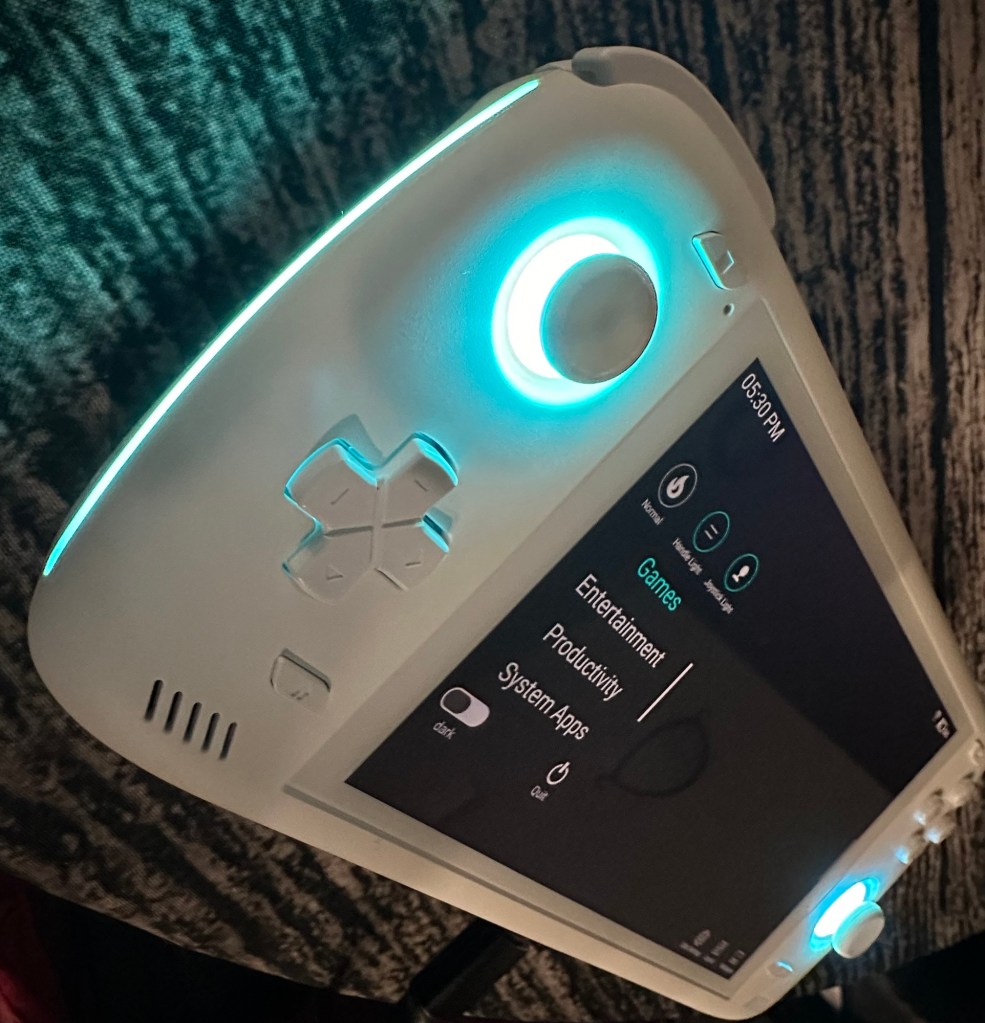
So the hardware is solid, how about the software? As mentioned Ayn has included everything you need to manage a device like this, and it’s all well implemented. Applets to change controller modes, and change key mapping, including mapping keys to the screen, are just a swipe away. The screen mapping utility in particular is extremely intuitive and seamless, allowing you to define screen zones and assign physical buttons and actions to them, which is a must on any mobile platform.

The only thing left to consider then is the viability of Android itself as a gaming platform. For emulation, everything up to the Dreamcast era is supported and effortless. Newer systems, unfortunately, simply have no pathway however, with no serious emulation efforts available on Android for PlayStation 3, XBox 360, WiiU or even classic XBox. Switch was doing incredibly well, with the Switch itself also being ARM, but… Yeah. That said, if more legacy emulation, and native Android games, suffice, it’s impossible to go wrong with the Odin 2 for handheld gaming. Especially considering that the whopping 8000mAh, combined with excellent Snapdragon efficiency, result in absolutely ridiculous battery life that just isn’t remotely achievable on x86 platforms, with over 10 hours of play time observed on a single charge during testing in both native games and GameCube emulation.
So if Android suits your use case, save yourself nearly $700 and get the Odin 2. Seriously, at roughly $500 for the Max configuration with 16GB RAM and 512GB internal storage, it’s an insane value. If your use case demands windows though, either because x86 games are your passion, or you want to emulate systems that just aren’t an option on Android, you’re going to have to reach a bit deeper. The question is, does GPD provide the answer at nearly $1200 (for the 32GB/2TB config)? Let’s find out…
The first thing you notice about the Win 4, after wondering whether Sony might have a lawsuit here over the Vita design, is its substantial weight and… girth. The device looks fairly small, and at 8.66 x 3.62 inches it is in fact a bit smaller than the Odin, but at 1.1 inches it’s substantially thicker, and at 1.3lbs (598g) a whole lot heavier as well. It’s built like a tank though, and similar to the Odin feels extremely high quality. In exchange for the heft you get a powerful package courtesy of the AMD Ryzen 7 8840u APU, 32GB quad channel LPDDR5x 7500 MT/s RAM, and 2TB PCIe Gen 4 NVMe for storage. So what does all of the impressive hardware deliver in terms of performance? It’s a surprisingly interesting question and in trying to answer it, the stark differences between Windows and Android, x86 and ARM, immediately become apparent as we realize we first have to ask “At what wattage?” This is something we don’t think about at all on Android, but on Windows will be a daily fact of life. To their credit, GPD provides a tool called “Motion Assistant”, that has continued to evolve decently well but remains a bit janky, to manage this critical aspect of the system. It isn’t nearly as polished as what Ayn provides for the Odin, but it works. We’ll talk more about software later, but for now here is the relevant bit.

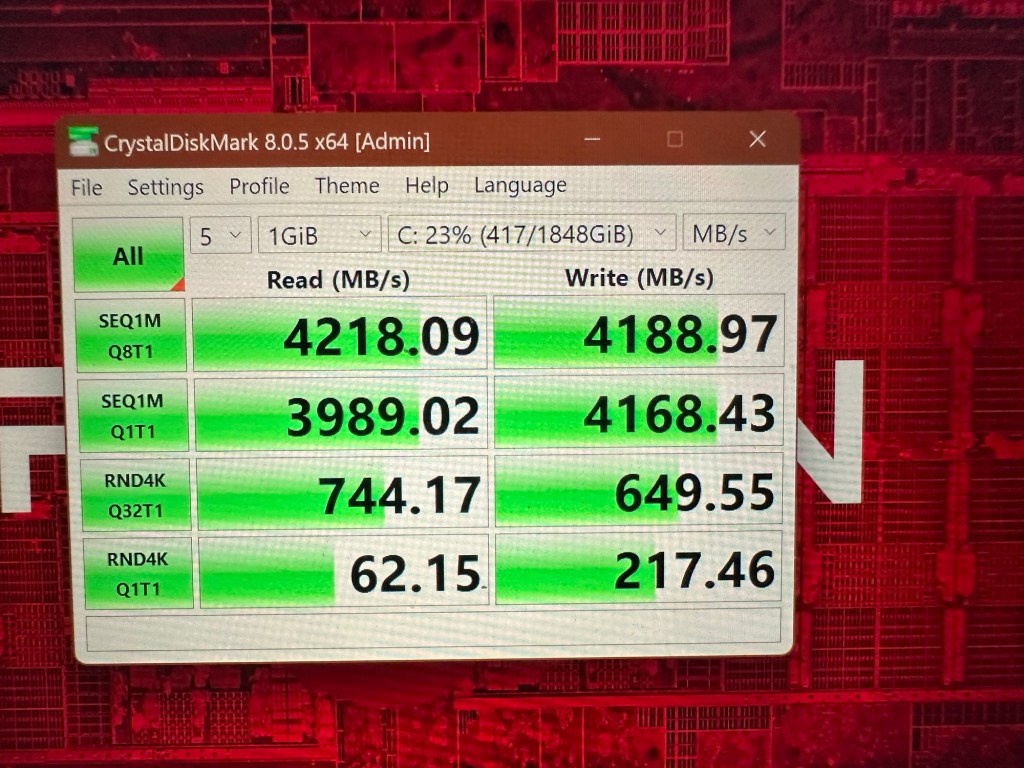
For testing purposes all tests were done twice, once plugged in at 30W APU TDP (30 watts supplied to the Ryzen 8840u) and once unplugged at 15W. So how much difference does it make? Well a fair bit really. Looking at disk performance, it’s not noticeable in the real world given the absolute performance on offer from NVMe, but it’s a very apparent ~20-40% in the benchmark.

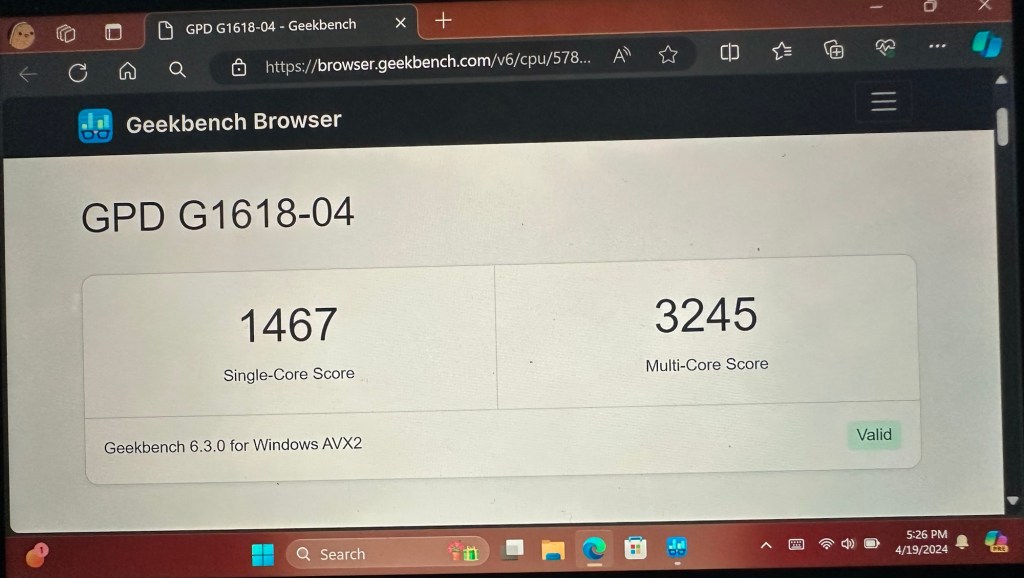
Moving on to CPU and GPU performance, the story is similar. Geekbench 6 was also used on Windows to give a sense of performance relative to the Snapdragon in the Ayn, although cross platform comparison is obviously more complex than suggested by synthetic benchmarks.
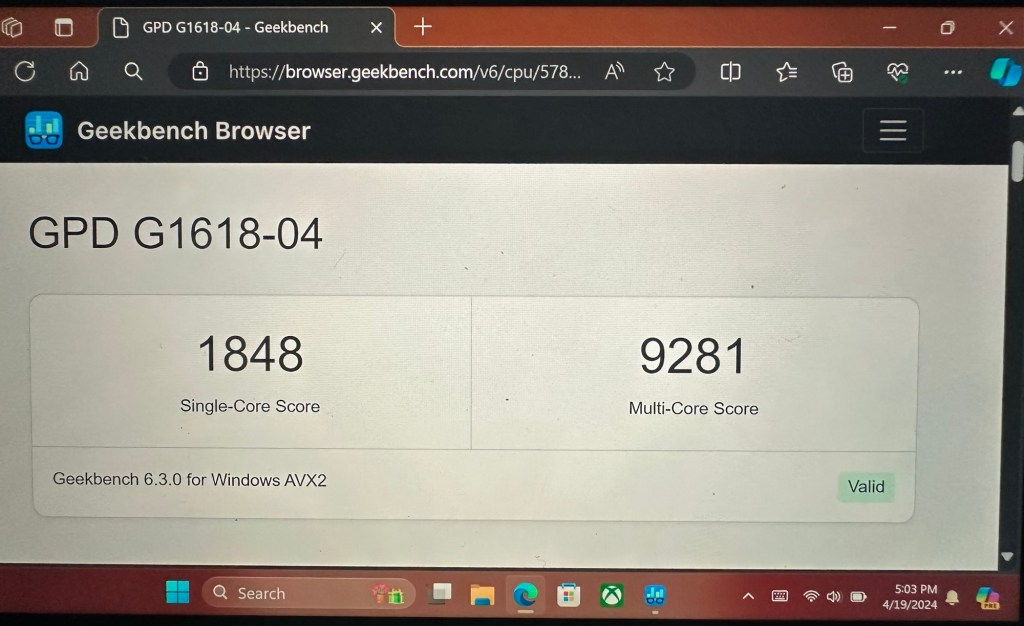
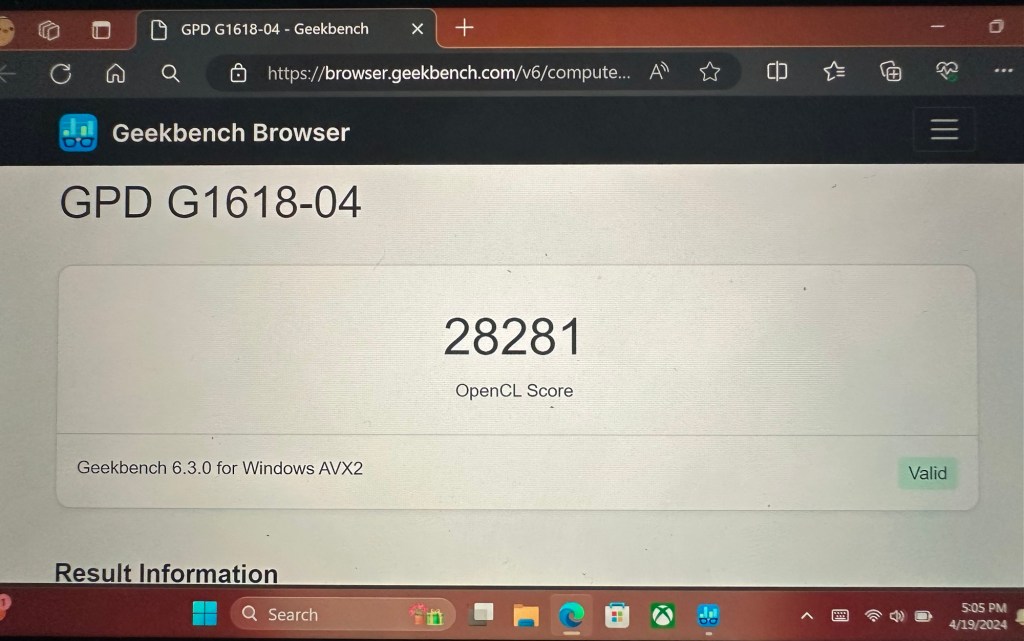
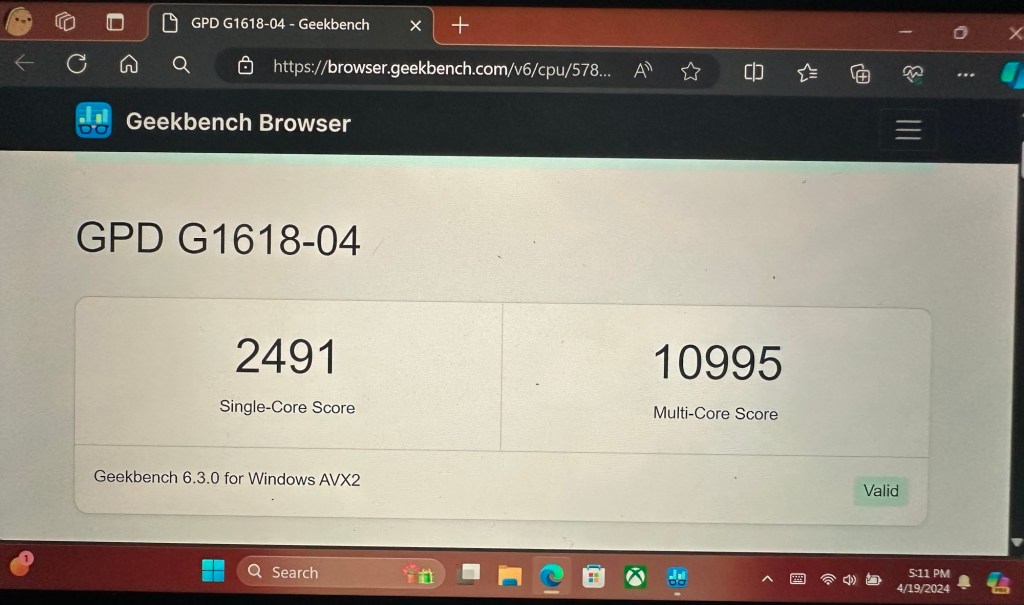

The main take away here is that as x86 goes, AMD has quite a good efficiency story to tell with the 8840u, offering significant performance at 15W, but even feeding the APU double the power at 30W doesn’t raise the ceiling too much. One could argue that diminishing returns kick at anything above 15W, but about 25W or so is probably all you need for the 8000 series if you want maximum performance. Testing limits in the other direction we can see that downward scaling is much more linear, with 5W still yielding surprisingly usable performance.

So we can see that at Snapdragon power levels, the Ryzen is delivering a bit less CPU performance, but solidly more GPU. Even given the differences before Windows and Android, this should result in reasonably solid battery life at acceptable frame rates.
Economics on the Win 4 are similar to the Ayn, with all controls feeling solid, a generous array of buttons including two on the rear, but a few notable exceptions. The first one is a negative. The analog sticks are solid and well implemented, but are not Hall type. This might not matter much, but is worth noting. On the positive side GPD has implemented a Windows Hello capable fingerprint sensor, which is a fantastic edition, and a shockingly good “finger mouse” that in practice actually exceeds the SteamDecks trackpad, and is surprisingly useful even on a touchscreen Windows device. The Win 4 has one more party trick though, which is the keyboard. It’s not necessarily a game changer, but it’s both better than one might think in terms of key feel, feedback and usability, and less useful than one might imagine given the plethora of buttons. One surprise was the keyboard and finger mouse enabled an interesting hybrid control approach in games like World of Warcraft that was quite effective. The 6” screen, even bumping the res down from the native 1080p to 720p, can make text and tiny UI elements too difficult to navigate though.



Controls aside, ergonomics aren’t as good as the Ayn Odin 2 mainly due to the significantly higher weight, and the shallowness of the rear grips, rendering longer gaming sessions much less comfortable on the Win 4. Audio is provided via front firing speakers that aren’t quite as good as the Ayn, with a lower threshold for distortion, and a 3.5mm headphone jack as well. By way of IO there are USBC ports top and bottom, and in a bit of a surprise, a questionably useful Oculink port for connecting an external GPU to PCIe. This will either be a dream come true, or something you literally never use, with not much in between. Personally I’d rather see USBA. Rounding out the physical packaging GPD also provides nice ambient lighting, in this case on the triggers, active cooling through top and rear vents via an (occasionally quite loud) internal fan and, in a final nod to the Vita, an attachment point for a lanyard.
Whether this is the better device overall again comes down to Windows vs Android. The Win 4 offers only a 4500mAh battery, slightly more than half that of the Ayn, and both the hardware, and especially the operating system, are far more power hungry. As a result, expectations really need to be tempered in terms of battery life. Locking the APU at 5W and the screen at 45Hz, really the absolute best case while still maintaining some level of usable performance, will yield about 5 hours of battery life. This is a significant difference made more significant by the fact that many native Windows games will struggle at this low TDP, even at absolute minimum detail levels, leaving native Android games, designed to work on a miserly power budget, ironically looking better.
In the final accounting, for basic emulation it’s impossible not to recommend the Odin as the clear winner here. The battery is massive and the processor and OS are efficient, meaning actual multi-day on a single charge gaming is a real possibility. If, on the other hand, Windows games, or Xbox/PS3 emulation, are an absolute must, the whole comparison is moot and the Win 4 is the only choice. What’s left then is a comparison of the Win 4 against its other x86 competitors, but this entry is already too long, so that will have to wait for another day!

